Institutional
Is Blockchain Privacy Normal? The Rise of Confidential Transfers and Privacy Tools
Blockchains exposed transaction data that traditional finance has always kept confidential which turned out to be a challenge for institutional adoption. A new layer of cryptographic tools across Ethereum, Solana, and dedicated privacy chains restores confidentiality while preserving on-chain auditability.
APR 29, 2026
Last updated APR 29, 2026 · V1
TL;DR
- Traditional banking, payroll, and settlement have always kept transaction data confidential. Public blockchains broke that norm by design.
- A new wave of protocol-level privacy is emerging. ERC-7984 on Ethereum, Confidential Transfers on Solana, Aztec Network, and Railgun are building privacy that coexists with auditability.
- Regulatory clarity is enabling compliant privacy. Tools like Private Proofs of Innocence and selective disclosure let users prove legitimacy without exposing full transaction histories.
- In Q4 2025 Zcash reflected renewed focus on privacy as a core primitive.
- Validators operating on chains adopting these standards play a central role in securing and processing confidential traffic. Everstake supports networks integrating these standards across Ethereum, Solana, and beyond.
Privacy as the Historical Default
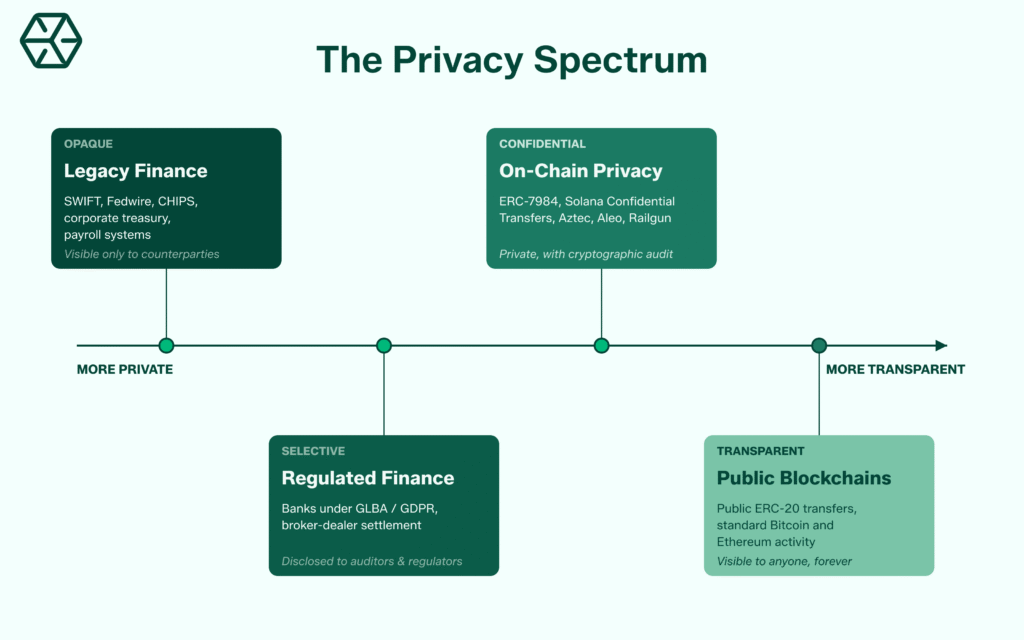
Financial privacy is the baseline assumption in traditional finance. A corporate treasury’s moves are protected by NDAs, broker confidentiality, and settlement systems that reveal details only to relevant counterparties and regulators.
Banking secrecy dates back centuries, and modern financial infrastructure inherits this tradition. The Gramm-Leach-Bliley Act in the US, GDPR in the EU, and similar frameworks worldwide enshrine confidentiality as a consumer right.
Commercial settlement via SWIFT, Fedwire, or CHIPS is opaque to the general public. Even publicly listed companies disclose financials on a delayed, aggregated basis.
A treasury team at a Fortune 500 company would typically not accept a payment system where every supplier invoice was visible to competitors in real time. In this case, privacy becomes a prerequisite for doing business.
Why Public Blockchains Broke Privacy
Public blockchains adopted complete transparency as a default. Addresses, amounts, timestamps, and counterparties sit on an immutable public ledger.
Auditability and verifiability by any party removes the need to trust intermediaries. It enables open permissionless networks where anyone can verify the rules are being followed.
For many early crypto use cases, especially individual adoption, this worked well enough. But transparency at the protocol level may be less fit for institutional workflows.
Default transparency blocks several institutional scenarios:
- Payroll on-chain exposes every employee’s salary to anyone who can identify the company wallet.
- Institutional settlement reveals position sizes, counterparties, and timing to competitors and front-runners.
- Treasury operations broadcast strategy shifts in real time.
- B2B payments expose commercial relationships, pricing terms, and vendor structures.
- DeFi strategies executed by funds become visible and copyable the moment they are submitted.
It introduced an extra structural bottleneck for institutional adoption. Capital that would otherwise flow to on-chain rails is either held back or might be routed through intermediaries that recreate privacy off-chain.
The New Wave of On-Chain Privacy
A new generation of privacy infrastructure is being built directly into leading smart contract platforms. These designs integrate confidentiality at the token and protocol layer.
ERC-7984: Confidential Tokens on Ethereum
ERC-7984 is a draft Ethereum standard for confidential fungible tokens. Co-authored by contributors from OpenZeppelin and Zama, the proposal introduces tokens where balances and transfer amounts are represented as encrypted ciphertext handles rather than readable numbers.
The standard is technology-agnostic in principle, allowing implementations on different cryptographic foundations:
- FHE (Fully Homomorphic Encryption): compute on encrypted data without decrypting it.
- MPC (Multi-Party Computation): jointly process data without exposing inputs.
- TEE (Trusted Execution Environments): hardware-based secure computation zones.
In practice, the current live reference implementation by OpenZeppelin and Zama is powered by FHE. Threshold MPC is used for key management. It is also stated to be quantum-ready.
In March 2026, GSR and Zama completed the first confidential OTC trade on Ethereum using Zama’s FHE protocol, executed between fully KYC-compliant counterparties. OpenZeppelin’s reference implementation provides the security assurance and tooling maturity that institutional deployments require.
ERC-7984 is not a replacement for ERC-20. It is a parallel standard designed for use cases where confidentiality is a requirement: payroll, institutional settlement, private DeFi strategies, and regulated finance.
Solana Confidential Transfers
On Solana, confidential transfers are implemented as part of the Token-2022 program via the Confidential Transfer extension. The extension uses zero-knowledge proofs and Twisted ElGamal encryption to hide transfer amounts while keeping the transaction verifiable on-chain.
- It was available as early as January 2024, when Paxos launched USDP on Solana with the extension enabled.
- In April 2025, Solana developers launched a broader suite called Confidential Balances, extending the functionality to shielded balances, mints, and burns. The system includes an optional auditor key: a single ElGamal public key can be set at the mint level, allowing a designated party to view amounts for compliance purposes.
- The ZK ElGamal Proof program is temporarily disabled on Solana mainnet and devnet pending a security audit. Confidential transfers are not executable today, though the design and tooling remain in place.
Paxos adopted the Confidential Transfer extension for its USDP stablecoin launch on Solana in January 2024, combining it with the Permanent Delegate extension to meet NYDFS requirements.
Aztec Network: A Privacy-First L2
Aztec Network architecture is built around private computation L2.
Contracts are written in Noir, a Rust-style language purpose-built for zero-knowledge circuits. Key milestones:
| Date | Event |
| May 2025 | Public testnet launch |
| November 2025 | Ignition Chain mainnet goes live with 185+ operators and 3,400+ sequencers |
| March 31, 2026 | Alpha mainnet with private smart contract execution |
| 2026 roadmap | Target ~6s block times on Alpha, with 3–4 second block times and continued decentralization by end of 2026 |
Aztec integrates privacy at three levels:
- Private data for confidential transactions.
- Private identity for selective disclosure.
- Private computation for on-chain behavior.
Checkpoints of Aztec blocks settle on Ethereum roughly every 72 seconds. Aztec remains in Alpha and the team has publicly disclosed a critical vulnerability.
A patch is planned for the v5 release in July 2026, and the project advises users not to deposit funds they cannot afford to lose at this stage.
Railgun: Privacy Middleware for DeFi
Railgun is smart contract infrastructure that brings privacy to existing EVM networks, including Ethereum, Polygon, Arbitrum, and BNB Chain. It is not a new chain.
Users shield assets into private balances using zk-SNARKs, then interact with DeFi protocols like Uniswap or Aave from within the shielded asset smart contract.
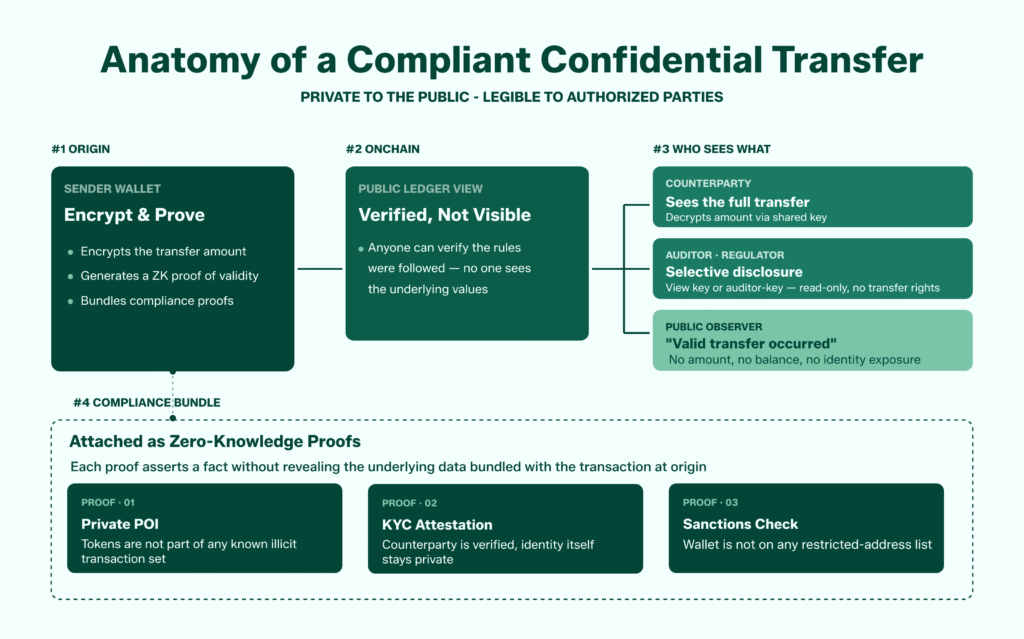
Railgun’s most important design feature from a compliance perspective is Private Proofs of Innocence (Private POI). When users transact from shielded balances using integrated wallets like Railway Wallet, a zero-knowledge proof is generated demonstrating that the tokens are not part of a known list of illicit transactions or sanctioned wallets.
The proof is created using only public data and preserves user privacy while providing cryptographic assurance of legitimacy.
Aleo: A Privacy-First Layer 1
Aleo is a Layer 1 blockchain built around zero-knowledge cryptography from the ground up. Founded by a team that includes Howard Wu, a former technical advisor to Zcash.
The architecture separates execution from verification. Users run applications off-chain in a zero-knowledge virtual machine called snarkVM, generating a proof of correct computation. Validators then verify the proof on-chain without seeing the underlying inputs. This preserves confidentiality for amounts, addresses, and program state while keeping the network verifiable.
Compliance is built in via view keys, allowing selective disclosure to auditors, regulators, or counterparties. In February 2026, Paxos launched a private stablecoin USAD on Aleo mainnet, targeting enterprise payroll and treasury use cases.
Aleo also partnered with Mercy Corps and GSR on a humanitarian aid pilot in Colombia in April 2026, using a private USDC variant called USDCx to deliver stablecoin support without exposing recipient data.
More and more privacy tools are expected to meet compliance standards.
Comparing the Privacy Tech
Not all privacy designs solve the same problem. The table below summarizes how leading approaches differ:
| Project | Chain | Privacy Tech | Model | Compliance Hook |
| ERC-7984 | Ethereum | FHE (live); MPC/TEE possible | Confidential token standard | Selective disclosure, auditor keys |
| Solana Confidential Transfers | Solana | ZK proofs, Twisted ElGamal encryption | Token extension | Optional single auditor key |
| Aztec Network | Ethereum L2 | zk-SNARKs, Noir circuits | Privacy-first L2 | Selective identity disclosure |
| Railgun | Multiple EVM chains | zk-SNARKs | Shielded middleware | Private Proofs of Innocence |
| Aleo | Own L1 | zk-SNARKs, off-chain execution | Privacy-first L1 | View keys, selective disclosure |
| Zcash | Own chain | zk-SNARKs (Halo 2) | Dedicated privacy coin | Optional transparent addresses |
Each approach reflects a different trade-off between integration depth, performance, and compliance. Institutional adoption depends on all of the privacy preserving frameworks maturing in parallel.
Proprietary AMMs: Privacy Demand Showing Up in Market Structure
Proprietary AMMs, sometimes called Prop AMMs or dark AMMs, are private liquidity venues operated by professional market makers. They use the same on-chain infrastructure as public DEXs, but pricing and inventory are controlled by a single firm rather than exposed via a public curve.
Adoption has been rapid, particularly on Solana.
According to The Defiant, roughly 40% of Jupiter aggregator volume has routed through Prop AMMs, and more than 60% of total Solana DEX volume in certain weeks has flowed through closed pools.
Why PropAMMs emerged:
- MEV protection: with no public pricing curve, front-running and sandwich attacks become far harder to execute.
- Tighter spreads: reduced adverse flow lets market makers quote prices approaching centralized exchange levels, with slippage reported as low as 0 to 0.5 basis points on major pairs.
- Size: large orders fill near mid-market without sweeping a public AMM curve.
- Cleaner settlement: trades still settle on-chain, preserving auditability without leaking pre-trade information.
Proprietary AMMs are a market-driven answer to the information asymmetry that full transparency creates. Parallel work is happening at the cryptographic level: FHE-based dark pools, such as those being designed around Zama‘s protocol, aim to process encrypted orders inside the AMM smart contract itself, removing MEV extraction surface without requiring trust in a single operator.
Regulatory Clarity Is Enabling Privacy, Not Blocking It
Regulation and privacy are not opposed, despite possible misconception. Regulators care about preventing illicit finance, not about surveilling ordinary commercial activity.
The US GENIUS Act was signed into law in July 2025 and established a federal framework for payment stablecoins. The CLARITY Act was passed by the House in July 2025 and is still progressing through the Senate, aiming to define SEC/CFTC jurisdiction over digital assets.
It contributes to a more defined US regulatory environment in which compliant privacy tools can operate.
Compliance-friendly privacy relies on three techniques:
- Selective disclosure: users can reveal specific transaction data to auditors, regulators, or counterparties without making everything public.
- ZK proofs for compliance: cryptographic proofs demonstrate facts like “this wallet is not sanctioned” or “this counterparty is KYC-verified” without revealing underlying identity.
- Viewing keys: hierarchical keys allow auditors or tax authorities limited read access without transfer authority.
These mechanisms mirror how privacy works in traditional finance.
What Privacy Tech Means for Validators
For validators, confidential transactions introduce new technical and operational considerations that go beyond running standard node software.
Several implications are already visible:
- Hardware and performance requirements may rise, since FHE operations are computationally expensive and ZK proof verification adds overhead to block production.
- Compliance certifications become more relevant, because institutions deploying assets on privacy-enabled chains need infrastructure partners whose operations meet standards like SOC 2 Type II and ISO 27001.
- Network-level privacy features such as encrypted mempools and private transaction relays affect how validators handle MEV and transaction ordering.
Everstake operates as a validator across Ethereum, Solana, and other networks where these standards are being adopted.
Backed by compliance-certified infrastructure built for institutional volumes, Everstake remains committed to strengthening network robustness while meeting the operational requirements that arise from evolving confidentiality needs.
Running nodes on chains implementing confidential transfer standards while maintaining certifications expected by institutional participants positions validators as meaningful contributors to the next phase of on-chain privacy infrastructure.
FAQ
Is on-chain privacy legal?
Privacy itself is legal in virtually every major jurisdiction. The legal question turns on how privacy tools are used, not their existence.
How is ERC-7984 different from ERC-20?
ERC-7984 tokens keep balances and transfer amounts encrypted at all times, while ERC-20 tokens store these as readable numbers. ERC-7984 is not ERC-20-compliant but provides wrapping mechanisms between the two standards.
Do Solana Confidential Transfers hide the sender and receiver?
No, they hide only the transfer amount. Sender and receiver addresses remain visible on Solana.
Can institutions use these privacy tools today?
Standards are at varying maturity levels. Solana Confidential Transfers are designed and used by regulated issuers like Paxos, though the underlying ZK ElGamal Proof program is temporarily disabled pending a security audit.
ERC-7984 has working implementations but remains in draft status, Aztec is in Alpha with disclosed vulnerabilities, and Railgun is in active production use.
How do validators fit into the privacy infrastructure?
Validators process and secure confidential transactions on chains integrating these standards. Validator operations require appropriate compliance certifications and hardware capacity for cryptographic operations.
Will privacy break blockchain auditability?
Modern designs preserve auditability through cryptographic proofs rather than plaintext visibility. Anyone can verify that the rules were followed, while only authorized parties can see the underlying values.
Are proprietary AMMs the same as privacy protocols?
No. Proprietary AMMs address pre-trade privacy and MEV protection but settle on-chain in readable form. They are an operational response to transparency rather than a cryptographic privacy layer. Projects combining proprietary routing with FHE or ZK-based execution represent a convergence of the two approaches.
Disclaimer
This article is provided for informational and educational purposes only. It does not constitute financial, legal, tax, or professional advice of any kind. Nothing in this content should be interpreted as a recommendation, solicitation, or endorsement to buy, sell, hold, stake, or interact with any cryptocurrency, token, protocol, network, or platform mentioned herein.
References to specific projects and any other third-party protocols, products, or tokens, are included solely to illustrate technical developments in the blockchain privacy landscape. These references do not constitute an endorsement, affiliation, recommendation, or partnership between Everstake and any such project, and Everstake makes no representations or warranties regarding the security, functionality, compliance status, regulatory treatment, or performance of any project discussed.
Share with your network